Member-only story
Cloud Security Architecture – Zero Trust Model
As we continue our series on Cloud Security I thought it would be useful to go over one of the most used ( and abused ! ) terms in Cloud Security architecture which is that of Zero Trust. Vendors and providers will be screaming its virtues and how its a game-changer for the new business model but very few people will be explain exactly what zero trust is.
Lets start with a few clarifications ; Zero Trust is not a product but a concept. Like the name says it revolves around providing security without relying on traditional network controls and moving towards an identity centric model
Zero Trust Model and how it changes things
With Zero Trust you forget upon relying on the trust that is created by where the user is coming from ( regardless of where the user is an application , an actual user, a service identity etc. ) and instead we move to an identity-focused model. Every access is validated , authenticated based on its context and other attributes
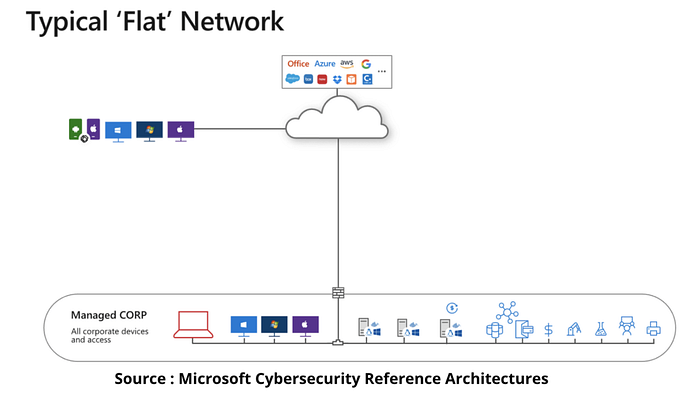
The below diagram gives an idea of how Zero Trust differs from your traditional model

Journey towards Zero Trust
Most companies have a traditional way of doing stuff ( even in 2022 ) where you have firewalls for ingress / egress traffic and limited segmentation within internal networks. This slowly became a huge issue with rise of personal devices , BYOD, wireless etc. and a single compromised endpoint potentially having access to other devices within the network. Most breaches were enabled due to one endpoint allowing access to others within a network with no or limited authentication
In a zero trust world access decisions will be base on a centralized identity centric policy where access will be given based on dynamically evaluating the context of each request. User location , device , time , risk score etc. all are evaluated and the identity essentially becomes the firewall which allows / disallows access.
Below is the end result of a fully Zero Trust environment taken from Microsoft Cyber-Security reference architecture which is a great starting point for implementing this journey in your organization.
